Piriform CCleaner is one of the most popular clean up tools used by PC users. The software company was recently acquired by security firm, Avast. But it is now in the spotlight for the wrong reasons.
According to Cisco's Talos, the installer of CCleaner, which was distributed through official download channels, on Avast's servers, was found to contain malware. Piriform has acknowledged the issue as real, and has apologised for the same. It says that a hacker from an unknown IP address was receiving data from v5.33 of Ccleaner and CCleaner Cloud version 1.07.3191, both of which had been modified illegally to collect data from 32-bit Windows systems. It indirectly says that 64-bit versions of CCleaner were not were not affected, (but it is not confirmed). The company says it is investigating the issue.
The infected EXEs were sending information such as the name of the PC, the list of all installed software and Windows Updates, currently running processes, and the MAC address of the 1st three network adapters. According to Malwarebytes, the infected CCleaner also checks whether the current user has admin privileges, and whether the system is a 64-bit PC. CCleaner reportedly has 5 million new users per week, so the damage which may be caused by the malware could be enormous.
What should you do?
Check whether you have Cleaner version 5.33.6162. If you have v5.33, download and install version 5.34 immediately, CCleaner Cloud version 1.07.3191 users need not worry as Piriform has already sent an auto update to fix the issue,
We also recommend scanning your system for malware. Use your antivirus and a secondary scanner like Zemana Antimalware, or Malwarebytes, or Emsisoft Emergency Kit.
I have a 64-bit PC, should I be concerned?
Well yes, we recommend a scan just to be safe. Why? Look at the screenshot below, it was taken from my 64-bit PC and it detected ccsetup533_slim.exe as Trojan.Floxif malware.
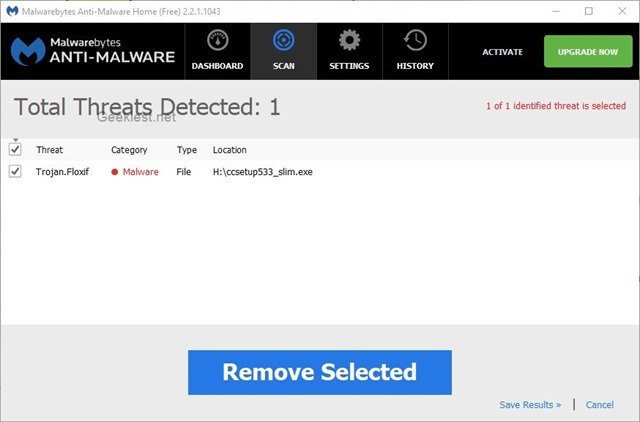
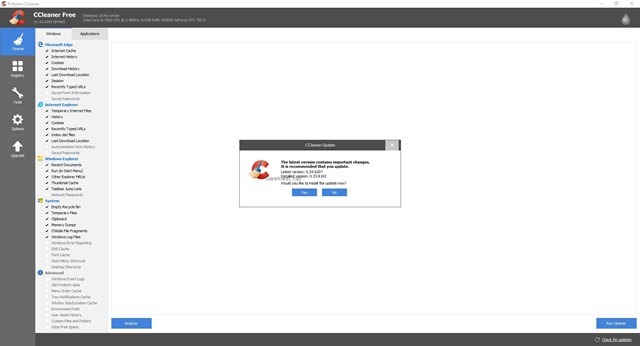
This is the Slim version of CCleaner v5.33 and it was affected, and I was using the application on my PC as is evidenced by the first screenshot you see here.