Piriform has updated CCleaner to version 5.35 just days after releasing 5.34. The reason? Well, as you may have read our previous article, a hacked version of CCleaner 5.33 was being distibuted from its official servers, which collected data from PCs it was installed on.
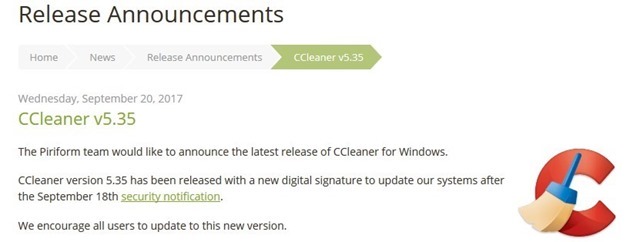
Now, a new statement posted on the Piriform website, says that "CCleaner version 5.35 has been released with a new digital signature", in order to update their systems. This may not much sense to users, as the original statement where the company announced the news, wasn't exactly a very transparent message.
However, if you had read Cisco Talos' findings, it clearly mentioned that CCleaner 5.33 had originally been digitally signed with a certificate from Symantec. But the hacked version had a similar certificate, but its timestamp showed it had been signed about 15 minutes later than the one previously released.
Cisco's post mentioned that " Ideally this certificate should be revoked and untrusted moving forward". So, it appears that Cisco was correct to say that, and Piriform has changed the certificate to ensure that a similar hack isn't done again.
The bigger question is, why did Avast (the parent company of Piriform) take almost a week to release an update, after it was notified by Cisco on September 13th. How many users were impacted by this? And who was behind this?
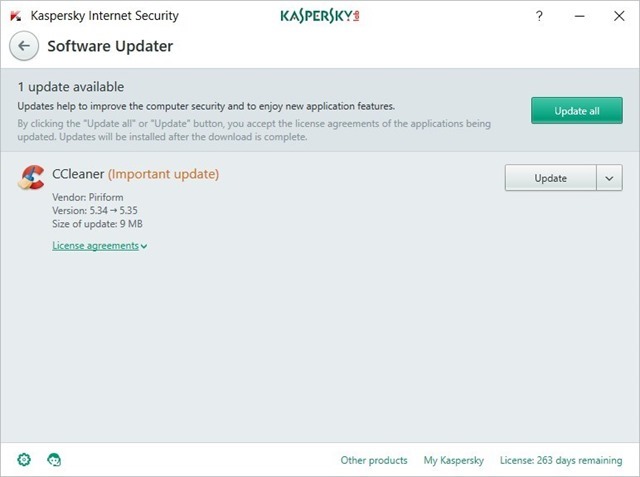
Funnily enough, Kaspersky popped up a notification today on my PC, asking me to update from 5.34 to version 5.35. Well played Kaspersky, that was right on the nose.